A while back, I wrote a short piece on the role patents hold for a small business. There are many solid reasons for seeking and gaining patent protection.
For a small, technical business, two of the larger reasons are to add value and to open lines of communication. But what about small businesses that are developing (or have developed) technology and are engaged in government contracting? It’s a challenging question.
I’m a skier. I’ve skied for most of my life and there are few runs on a mountain that I cannot tackle, albeit some at a slower pace than others. I’m fond of steep, double black diamond runs followed by an easy stroll through a glade. Few crowds and great snow.
What does this have to do with patents? It’s a good analogy. Patents, like skiing, are not for everyone. From an analogy point of view, most companies venturing into gaining patent protection are diving down a green slope and graduating to a strong intermediate blue. Companies may become well-versed in the process as they capture and protect their intellectual property. Hitting and navigating the “bumps” is part of the ride.
But throw a government contract into the mix and we are turning down a run marked “experts only” and “unmarked obstacles.” And like many double black diamond runs, the initial slope is gradual and inviting just before it drops off like a cliff. Why else would one such run be named “Devil’s Crotch”? If only the titles of government contracts were so informative.
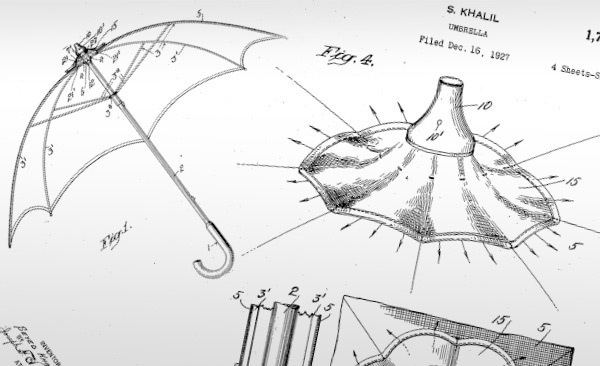
The fundamental purpose of a patent is to provide the inventor, for a limited period, with protection from would-be infringers for their new and useful invention. In exchange for the inventor disclosing the invention and meeting the requirements of patentability, the government grants them the right to exclude others from making, using, selling, manufacturing and importing that which is claimed in the patent.
A patent, as a form of intellectual…
KISS PR Podcast Story Source link
This is the "wpengine" admin user that our staff uses to gain access to your admin area to provide support and troubleshooting. It can only be accessed by a button in our secure log that auto generates a password and dumps that password after the staff member has logged in. We have taken extreme measures to ensure that our own user is not going to be misused to harm any of our clients sites.
We are an award-winning platform that caters to small businesses, content creators, and resellers, offering them the opportunity to enhance their content’s reach through its robust ecosystem. Businesses can submit press releases, share their personal or business brand’s narrative, announce new products, and leverage social media for broader distribution. We help expand your reach & assist you accurately gauge the effectiveness of your public relations efforts that fortifies your brand identity.